Routing Firewall logs to Splunk using Cribl
Let’s demonstrate a use case where we COLLECT syslog output from a firewall (pfSense) REDUCE, TRANSFORM, and then ROUTE it to a SIEM (or two) using Cribl. Maybe we’ll ENRICH it along the way.
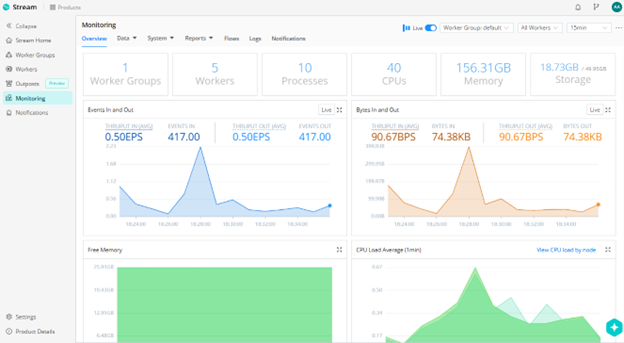
Cribl Stream Monitoring
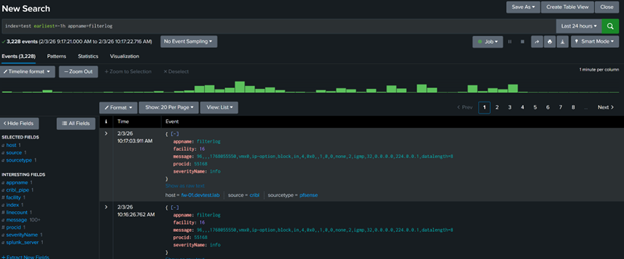
Initial ingest of pfSense logs into Splunk
There are some very basic fields already available, but several more are still in the 'message’ field waiting to be pulled out.
Several other fields remain unparsed in the message field. Let’s pull them out.
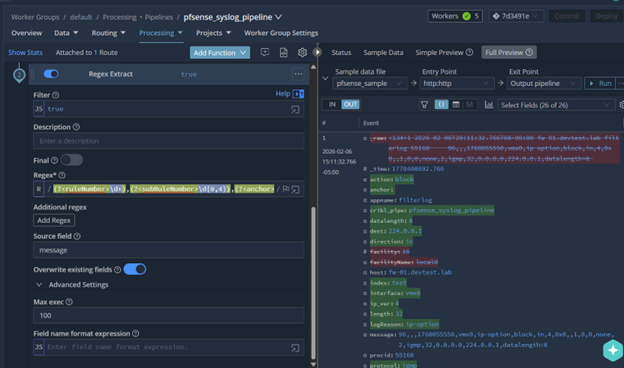
Cribl pipeline Regex Extract function.
However, since the syslog events are in the standard CSV format, the better option is to use a Parser function as it is more efficient. Regex is better suited for lesser or un- structured data.
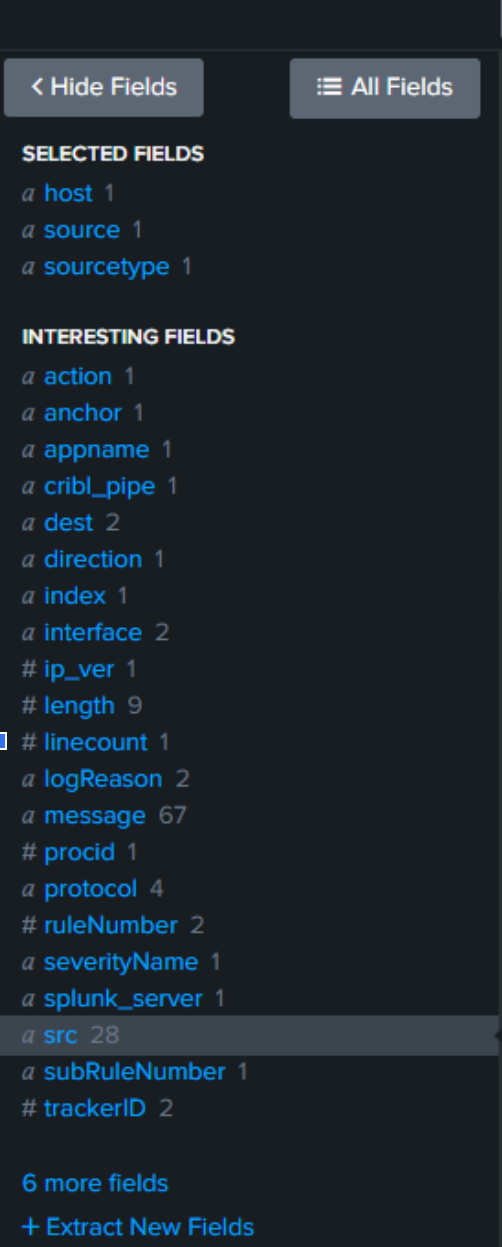
Look at all those fields!
We can now see our extracted fields. Map these to the Common Information Model (CIM) for bonus points.